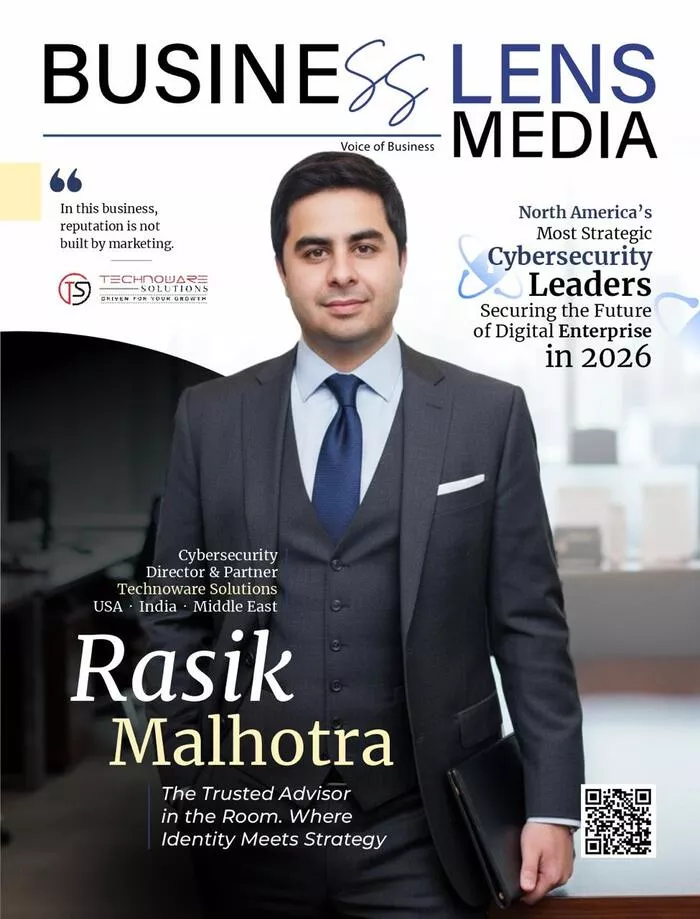
Inside Rasik Malhotra’s mission to help enterprises master identity governance, cloud security, and the AI agent sprawl redefining cybersecurity in 2026
Every enterprise, regardless of its size, sector, or geography, is built on a set of invisible decisions about trust. Who is allowed to access what. Which systems talk to which other systems. What happens when an employee leaves, a contractor’s engagement ends, or a business unit spins up a new cloud workload overnight. These decisions are not made once; they are made thousands of times a day, across every application, every database, every endpoint in the organization.
For decades, the discipline responsible for managing those decisions, Identity and Access Management, and its governance cousin, Identity Governance and Administration, operated in relative obscurity. It was considered a back-office function. IT plumbing. A compliance checkbox that mattered during audits and was largely forgotten between them.
That era is over.
In 2026, identity governance has become the single most consequential discipline in enterprise cybersecurity. The reasons are compounding. Cloud adoption has dissolved the traditional network perimeter. Hybrid workforces have made static access policies obsolete. Regulatory pressure around data privacy, access transparency, and audit readiness is intensifying across every major market. And now, the rapid proliferation of autonomous AI agents has introduced a category of non-human identities that existing governance frameworks were never designed to handle. The enterprise identity landscape is more complex, more exposed, and more strategically important than at any point in the history of modern computing.
Navigating this landscape requires more than technology. It requires advisors who understand the discipline at a depth that cannot be assembled from certifications and product manuals. It requires consultants who have seen identity governance succeed and fail across industries, geographies, and technology generations. That is the space occupied by Rasik Malhotra, Cybersecurity Director & Partner at Technoware Solutions, and it is why some of the world’s largest enterprises turn to him when identity becomes the problem that nobody else in the room can solve.
A Career Built on the Discipline Nobody Wanted
Rasik Malhotra entered the identity and access management space more than sixteen years ago, at a time when the discipline barely existed as a recognized career path. The products that now anchor the IGA market like SailPoint, Saviynt etc. were either nascent or not yet conceived. There were no mature frameworks, no established best-practice libraries, and very few practitioners who understood the long-term strategic significance of what they were building.
Most technologists at the time gravitated toward the more visible and better-funded areas of cybersecurity: network security, endpoint protection, perimeter defense. Identity management was considered unglamorous. It was provisioning. It was directory services. It was the work nobody talked about at conferences.
Rasik Malhotra chose it anyway.
“I saw something that most people missed early on. Every security incident, every compliance failure, every data breach, when you traced it back far enough, you found an identity problem. Somebody had access they should not have had. An orphaned account was never deprovisioned. A service account was shared across teams with no oversight. The root cause was always identity. I decided that if I was going to spend my career in cybersecurity, I was going to spend it at the root.”
That decision, made when identity governance was still considered IT plumbing, is what separates Rasik Malhotra from the consultants and firms that have entered the space more recently. He did not arrive at IGA because the market got hot. He has been living inside its evolution, working with the platforms as they matured, advising enterprises as their identity challenges compounded, and developing the kind of pattern recognition that only comes from having done this work, at depth, across multiple market cycles and technology generations.
Technoware Solutions: Why the Consulting Model Matters
The cybersecurity consulting market is awash with firms that list identity governance among their service offerings. The problem, as Rasik Malhotra sees it, is that most of them treat IGA as one line item on a broader menu, something to be staffed with generalists and delivered against a template. That approach produces implementations. It does not produce identity programs.
The distinction matters enormously in practice. An implementation connects systems, configures connectors, and delivers a working deployment. A program designs the governance model that determines how access is requested, approved, reviewed, certified, and revoked across the organization. It defines role structures. It establishes risk-based access policies. It builds the operational processes that sustain the program after the consultants leave. Without that governance layer, even the most technically elegant IGA deployment becomes shelfware within eighteen months.
Technoware Solutions was built specifically to deliver the program, not just the platform. The firm operates across the full spectrum of enterprise identity technologies, Microsoft Entra ID, Saviynt, SailPoint, Omada, Oracle Identity Governance, Pathlock etc. but Rasik Malhotra is clear that platform expertise is the starting point, not the differentiator. What sets Technoware apart is the consulting methodology: a structured, lifecycle-driven approach that starts with business process analysis and identity posture assessment, moves through architecture design and implementation, and extends into managed services and continuous optimization. The firm calls it embedded strategic partnership, and it means that senior expertise is present across every phase, not just the kickoff presentation.
“The biggest mistake enterprises make with IGA is treating it as a technology project. They buy a platform, they hire a systems integrator, they configure it, and they think they are done. Eighteen months later, access reviews are being rubber-stamped, orphaned accounts are accumulating, and the CISO is asking why the program is not delivering value. The answer is almost always the same: nobody built the governance. Nobody designed the operating model. Nobody thought about what happens after go-live.”
That philosophy has earned Technoware a client roster that includes Fortune 100 enterprises across banking, healthcare, biotechnology, media, logistics, and government. The firm has been named among the most promising IGA service companies and recognized as a thought leader in the IAM space. Rasik Malhotra’s continued proximity to client delivery, personal involvement in solution architecture even as the practice scales, has made him a trusted advisor to CISOs and security leaders navigating the most complex identity transformations in the market.
The State of IGA and IAM: What Has Changed, and What Enterprises Still Get Wrong
The identity governance landscape of 2026 bears almost no resemblance to the one Rasik Malhotra entered sixteen years ago. The technology has matured enormously. Cloud-native IGA platforms now offer capabilities that would have been unimaginable a decade earlier: AI-driven access recommendations, automated lifecycle management, continuous compliance monitoring, risk-based certification campaigns, and identity analytics that can surface anomalous access patterns in real time.
Yet despite these advances, Rasik observes that many enterprises are struggling with the same foundational challenges they faced years ago, just at a larger scale and with higher stakes.
The first is what the industry calls the entitlement sprawl problem. As organizations adopt more SaaS applications, more cloud infrastructure, and more interconnected platforms, the number of access entitlements per user has exploded. The average enterprise employee now has access to dozens of applications, each with its own permission model, role structure, and access provisioning workflow. Without a unified governance layer, this sprawl creates a massive and largely invisible attack surface. Every unnecessary entitlement is a potential lateral movement path for an attacker.
The second is the access review fatigue problem. IGA platforms have made it technically possible to conduct access certification campaigns at scale. But in many organizations, the sheer volume of reviews has turned the process into a rubber-stamping exercise. Managers approve access requests without examining them because the cognitive load of evaluating hundreds of entitlements across unfamiliar applications is simply too high. The review happens on paper. The governance does not happen in practice.
The third, and newest, is the non-human identity problem. Service accounts, API keys, bot credentials, and now AI agent identities have proliferated across enterprise environments. Research indicates that non-human identities already outnumber human identities in most large organizations by a significant margin. Yet the governance frameworks, the review processes, the lifecycle management workflows that enterprises apply to human users have not been extended to these machine identities. In many cases, nobody even knows how many exist.
“I tell clients: show me your non-human identity inventory. Who owns each service account? When was the last time its permissions were reviewed? What happens to its credentials when the project it supports is decommissioned? In most organizations, the honest answer to every one of those questions is ‘we do not know.’ That is not a minor gap. That is a governance failure hiding in plain sight.”
Rasik Malhotra’s consulting approach addresses these challenges at the design level, not as afterthoughts. His team builds identity programs that incorporate entitlement rationalization from the start, design access review workflows that are contextual and manageable rather than exhaustive and ignored, and establish governance models that treat non-human identities with the same rigor applied to human users. It is unglamorous, detail-intensive work. It is also the work that determines whether an identity program actually reduces risk or merely produces compliance artifacts.
AI Agent Sprawl: The Identity Crisis That Arrived Faster Than Anyone Expected
If entitlement sprawl and access review fatigue represent the chronic conditions of enterprise identity governance, AI agent sprawl is the acute crisis. The speed at which autonomous AI agents have entered enterprise environments has caught most organizations unprepared, and the identity implications are unlike anything the industry has faced before.
The nature of the problem is fundamentally different from managing human identities or even traditional service accounts. A service account, for all its governance shortcomings, is at least static. It connects System A to System B with a defined set of credentials and a predictable operational pattern. An AI agent is dynamic. It reasons. It makes decisions. It chains tool calls across multiple systems. It spawns sub-agents to handle subtasks. It can, depending on its architecture, escalate its own access privileges or access data sources it was not originally provisioned for. And it does all of this at machine speed, far faster than any human review process can monitor.
The emerging Model Context Protocol standard, which enables AI agents to interact with external tools and data sources through standardized interfaces, has added another layer of complexity. MCP connections carry real authority. They allow an agent to retrieve data, trigger workflows, and act inside critical systems without a human in the loop. When those connections are poorly governed, and in most enterprises they are barely governed at all, they become high-value access paths that can be exploited at machine speed.
This is the challenge Rasik Malhotra is now spending a significant portion of his advisory practice helping enterprises understand and address.
“The fundamental problem with AI agent sprawl is that it does not look like a security problem on the surface. It looks like a productivity initiative. A business unit deploys an agent to automate a workflow. It works. Nobody files a security review because nobody thinks of the agent as an identity. But it is an identity. It has credentials. It has access. It makes decisions. And when it is compromised, or when it behaves in ways nobody anticipated, the blast radius can be enormous because nobody governed it as an identity in the first place.”
Rasik Malhotra’s framework for advising clients on AI agent governance is built on five pillars. First, visibility: organizations must establish a comprehensive inventory of every non-human identity in their environment, including AI agents, and understand what each one can access. Second, lifecycle management: agent credentials must be provisioned, reviewed, and deprovisioned with the same discipline applied to human users. Third, least-privilege enforcement: agents must be granted only the minimum access required for their specific task, with purpose-bound, time-limited credentials that expire automatically upon task completion. Fourth, behavioral monitoring: continuous observability must be established to detect when an agent deviates from its expected operational pattern. Fifth, accountability: every autonomous action must be traceable to a responsible human identity who owns and is accountable for the agent’s behavior.
These are not theoretical principles. They are the methodologies Technoware is actively implementing with enterprise clients who recognize that the window to establish AI agent governance is narrow and closing.
How AI Is Transforming Identity Governance for the Better
The conversation around AI and identity governance is not exclusively about risk. Rasik Malhotra is equally emphatic that AI represents the most significant capability upgrade the IGA discipline has ever received, and that enterprises that fail to leverage it will find themselves unable to keep pace with the scale and complexity of modern identity environments.
The traditional model of identity governance was built around periodic, manual processes. Access reviews happened quarterly or semi-annually. Entitlement analysis was conducted by consultants during assessment engagements. Risk identification depended on auditors reviewing access reports after the fact. This model was always reactive, always lagging behind the pace of organizational change, and always dependent on human bandwidth that was never sufficient for the scale of the problem.
AI has fundamentally altered this equation. Modern IGA platforms now embed machine learning capabilities that enable continuous access monitoring, real-time anomaly detection, intelligent access recommendations, and automated risk scoring that can prioritize remediation without waiting for a scheduled review cycle. Microsoft Entra ID uses AI to deliver risk-based conditional access and intelligent lifecycle recommendations. Saviynt’s identity cloud leverages machine learning to detect access outliers and automate certification workflows. SailPoint’s platform applies behavioral analytics and natural language processing to surface hidden governance gaps.
For a visionary like Rasik Malhotra, these capabilities do not replace the advisory work. They amplify it. AI handles the pattern recognition and anomaly detection at a scale no human team can match. The consultant’s role shifts to designing the governance frameworks that contextualize what the AI surfaces, defining the risk models that determine how alerts are prioritized, and building the operational processes that translate automated intelligence into organizational action.
“AI has given identity governance professionals something they never had before: the ability to see everything, continuously, in real time. But seeing is not governing. Governance is what you do with what you see. That is where deep domain expertise becomes irreplaceable. The AI can tell you that an access pattern is anomalous. It takes a seasoned practitioner to understand why it is anomalous, what the business context is, and what the right remediation looks like. That judgment cannot be automated.”
Advising Across Borders: How Three Markets Shape One Practice
Technoware’s advisory practice operates concurrently across three of the world’s most demanding markets for identity governance: the United States, India, and the Middle East. This is not a sequential expansion story. It is a deliberate strategy to serve clients across diverse regulatory, cultural, and technological landscapes simultaneously, because the insights generated in each market directly strengthen the advisory work delivered in the others.
The US market is defined by its regulatory density. Enterprises operating under HIPAA, SOX, GLBA, CCPA, and an accelerating wave of state-level privacy legislation need identity programs that are not merely technically functional but audit-ready and defensible under regulatory scrutiny. Technoware’s US engagements focus heavily on governance model design, access certification methodology, and building identity programs that can withstand the questions regulators and auditors will inevitably ask.
India presents a different set of challenges: massive scale, deeply heterogeneous technology environments, and digitization mandates that demand identity programs capable of governing hundreds of thousands of identities across complex organizational structures. Rasik Malhotra’s decade of experience in this market has given him an instinct for designing governance architectures that perform at volumes that would overwhelm programs designed for smaller environments.
The Middle East, and the UAE in particular, is where Rasik Malhotra sees the most forward-looking identity work happening globally. Driven by ambitious national digital strategies, governments and enterprises in the Gulf are building cloud-native identity architectures from the ground up, unconstrained by the legacy technology decisions that slow transformation in more established markets.
“Every market teaches you something different. The US teaches you regulatory rigor. India teaches you how to govern at extraordinary scale. The Middle East teaches you what is possible when you start with a blank canvas and genuine ambition. I bring all three perspectives into every client engagement, regardless of where the client sits. That cross-pollination is one of the most valuable things Technoware offers.”
Cloud Security Through an Identity Lens
A recurring theme in Technoware’s advisory work is helping enterprise security teams reframe how they think about cloud security. His argument is direct: cloud security and identity governance are not parallel disciplines. Identity governance is the foundation on which cloud security is built. Without it, every other cloud security investment is compensating for a gap that should not exist.
In hybrid and multi-cloud environments, where organizations operate across Azure, AWS, Google Cloud, and on-premises infrastructure simultaneously, the absence of a unified identity governance layer creates exactly the conditions that sophisticated attackers exploit: fragmented access policies, orphaned accounts, inconsistent entitlement models, and visibility gaps across cloud boundaries. The attack surface in a modern enterprise is no longer defined by its network topology. It is defined by its identity topology.
Rasik’s methodology integrates identity governance into the foundational architecture of cloud deployments: single sign-on, conditional access, entitlement management, lifecycle automation, and Identity Threat Detection and Response capabilities, all woven together under Zero Trust principles. For his clients, this is not an aspirational framework. It is the operating model Technoware designs and implements in production environments.
“I ask every client the same question at the start of a cloud security engagement: can you tell me, right now, who has access to what across your entire hybrid environment, and why? If the answer is no, and it usually is, then that is where we start. Everything else, the CASB, the CSPM, the microsegmentation, all of it is downstream of that question.”
Looking Ahead: Where the Industry Is Heading
Rasik Malhotra is measured but direct about where he sees the identity governance landscape heading over the next several years.
Platform consolidation will accelerate. The era of managing separate tools for human IAM, privileged access management, cloud entitlements, and non-human identity governance is unsustainable. Enterprises will demand unified platforms, or at minimum unified governance layers, that provide visibility and control across every identity type from a single operational model.
Identity governance and security operations will converge. The notion that IGA is a compliance function and threat detection is a SOC function will give way to integrated identity security architectures where Identity Threat Detection and Response, security posture management, and continuous access analytics operate as a seamless whole.
Regulatory mandates for AI agent governance will arrive, and they will arrive faster than most organizations expect. The enterprises that have already built governance frameworks for non-human identities will have a decisive advantage. Those caught retrofitting after mandates take effect will face the most challenging compliance scramble the industry has seen since the early days of SOX.
And the demand for deep IGA consulting expertise will intensify. As identity governance moves from a compliance exercise to the strategic core of enterprise security, organizations will increasingly recognize that this is not work that can be staffed with generalists or outsourced to firms that treat identity as one offering among dozens. The market needs practitioners with genuine depth, people who have lived inside the discipline across technology generations and can guide enterprises through the complexity with confidence and precision.
“The next few years will separate the organizations that invested in identity governance as strategy from those that treated it as a checkbox. The technology will keep evolving. The threats will keep compounding. The regulations will keep tightening. In that environment, the organizations that built strong identity foundations will operate with confidence. The rest will be reacting to crises they could have prevented.”
On Leadership: Depth Over Scale
Rasik Malhotra’s leadership philosophy runs against the grain of the consulting industry’s prevailing growth model. In a market where most firms scale by hiring fast, staffing with generalists, and optimizing for utilization rates, he has chosen a different path: build a team with genuine domain depth, stay close to the work, and let the quality of the advisory output speak for itself.
He remains deeply involved in solution architecture and client delivery at Technoware, a choice he views not as a failure to delegate but as a competitive advantage. The most consequential decisions in an identity governance program, the ones that determine whether the program thrives or fails in production, are made in architecture sessions, design reviews, and governance workshops, not in executive steering committees. Rasik Malhotra’s presence in those rooms is what clients pay for, and it is what they remember.
He is also candid about the talent challenge the industry faces. The identity governance discipline demands a rare combination of technical depth, regulatory fluency, business strategy, and the communication skills to translate complex identity architectures into language that resonates with boards and audit committees. Practitioners with that full range of capability are exceptionally scarce. Building that bench, through mentorship, hands-on development, and a culture that values depth over speed, is central to Technoware’s long-term vision.
“In this business, reputation is not built by marketing. It is built engagement by engagement, architecture by architecture, client by client. You either deliver work that stands up under real-world pressure, or you do not. There is no shortcut for that. And there should not be.”
The cybersecurity industry is at an inflection point that will define the next decade of enterprise security. Cloud, AI, autonomous agents, and an increasingly adversarial threat landscape have converged to make identity governance the most strategically consequential discipline in the field. It is no longer a supporting function. It is the discipline that determines whether everything else in the security stack actually works.
For sixteen years, Rasik Malhotra has been advising enterprises on how to get identity right. He started when nobody was paying attention. He stayed when the work was unglamorous. And now, as the rest of the industry arrives at the conclusion he reached long ago, that identity is everything, he is the advisor organizations call when they need someone who has done this before, at depth, at scale, across the most demanding environments in the world.
The moment has caught up to the man. And the man has been ready for a very long time.
ABOUT
Rasik Malhotra is the Cybersecurity Director & Partner at Technoware Solutions, a specialized cybersecurity consulting practice serving Fortune 100 enterprises and organizations across the United States, India, and the Middle East. With over 16 years of domain expertise in Identity Governance and Administration, Cloud Security, and AI Security, Rasik Malhotra and his team advise and implement comprehensive identity programs across platforms including Microsoft Entra ID, Saviynt, SailPoint, Omada, Pathlock and Oracle Identity Governance. Technoware has been recognized as a thought leader in the IAM space and named among the most promising IGA service companies.
Website: www.technoware.solutions